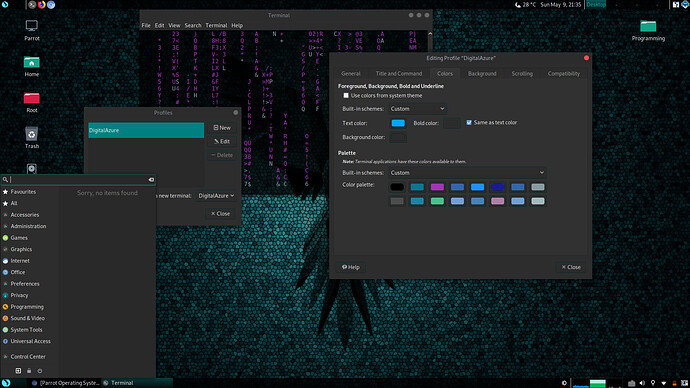
super + t key opens 2 terminal, IDK if its a bug or some config issue. not a big one but…thought point it out 




yeah it loads the default Parrot Terminal and that in distorted form
Sorry dmknight its PIA, not Proton. Sorry same shit different toilet, my bad bro!! It uses that node and instead of FrozenDNS its PIA’s DNS configs, I looked into it before on my phone and ProtonVPN has a free version and you can also select that same exit IP which is a TOR node, now I dont know if its still that way, or how offten they get a new IP and if its always that same one, I’m sure it gets blacklisted offten and needs changing allot if many are using it.
That to me looks like lots of nefarious actions are going on there cause how coincidental is it for PIA ProtonVPN AnonSurf and TOR just all happen to use that same IP and all of these programs have the same thing in common at the core and thats obscurity regardless of how they reach that point. Anon-surf on github is called Kali-anonstealth and has different configurations for people who dont use resolvconf and has default DNS of PIA plus you could use I2P if that still has support ive no idea, but yea its a exit point in Norway or Sweden I forget the exact country.
You either are not aware of those details or just dotn have a need to install kali and get anonsurf off github for it. Which I totally respect bro, cause im not talking about the protonvpn’s actually vpn you get for free on android or windows, I literally mean the version of anon surf running around using PIA’s sorry and not protonVPNs exit node in norway or sweeden one of those two and exits using that tor-node/socks5 and thats what I ment I just didnt complete my thought enough to words on the forum to really drive that point. Thats why I ased whats the difference? I wasnt asking a question, I was more or less making a statement, do you know what mean now? I dont have that problem when I configure my own socks5 (not default settings) to use on ips I chose to use in conjuction with tor. I’m far from perfect, and dont follow that “i’m better then all of you because I use arch linux” but they know what thier doing over at blackarch and theres more tools on that OS then on kali and parrot togther I think, and none that ive found yet obscure anything. Which says to me, you need to do that yourself, with whatever function you do it with, done by you and just you. Which says to me, only do that stuff when you know what your doing and do not use baked in OS programs because your going to have problems when you use somthing you didnt make yourself. Not that I made the socks5 protocol, but I know what doing when I utilize it, using my own config file.
So thats what I was saying, though it came out as a question as if I didnt know what the difference was. Weather its TOR, or IPA or I2P or ProtonVPN or my own socks5 proxychain using my own config file, if im exiting the IP related to all of those technologys and thats the only thing anyone can see or trace it back to, whats the differance how I got there if the end result is identical in every technology listed that uses 10.252.0.0/10 (which should be an internal IP but thats what is listed in the config file for kali-anonstealth)or something close to that, whats the difference if thats the only piece leaked from me?
Now you get what I mean lol?
excuse me, anonsurf is called what?
is anonsurf obscure about how it reaches the point?
https://nest.parrotsec.org/packages/tools/anonsurf/-/blob/master/binaries/anonsurf
please read this source code, because anonsurf is one software i wrote some time ago and it has nothing to do with kali-anonwhat and any other anonsurf clone born during all these years
if you read the source code of the official anonsurf script it is pretty simple:
it does some checks and asks the user if to clean the system and kill some applications or not
it starts the tor daemon making sure to use the anonsurf torrc, and the tor daemon as the dns resolver
it sets some iptables rules to:
allow the tor daemon to access clearnet
route all the tcp traffic through tor transproxy
route all dns traffic (tcp and udp) through the tor dns resolver
drop everything else
it is extremely simple, and we decided to keep it written in bash to make it easier for everyone to just open the file and read what’s inside without hassle
other unofficial anonsurf clones do things in an obscure way? sincerely i don’t see why i should care, and i also don’t see why you should use them (the official anonsurf does not use resolvconf daemon to work, it actually takes care of disabling it while working)
so now the quality of an operating system is determined by the number of tools pre-installed…
i’ll tell you a story, and that story is mine, the story of a guy who loves the work done on blackarch by its developers and strongly respect the passion and the effort they put into developing such an awesome and properly crafted environment on top of such a lack of standardization which is arch, a distro i love and know since decades, but which fuckin’ lacks standardization and reliability, a distro that makes easy to users to customize things, and that makes hard for derivative developers to do a good job easily. and yet the blackarch developers managed to stay alive for years and craft a very nice distro.
back to the tools: more is NOT better, and as a professional penetration tester i can write it to you on top of an officially signed statement and allow you to show it to whoever you want because it is the fuckin’ truth!
if you pay more attention while you use blackarch, you would easily notice that many of such tools are either a bunch of bash scripts that nobody knows or nobody really use in real life, many of them are very old and unmaintained, many of them lack a proper quality analysis and some of them are even broken and require some manual hacks in order to work
NOTE: i’m talking about some of these tools, those which makes the numeric difference between blackarch and i.e. kali. the first of you who tries to say that what i wrote is that blackarch is broken, will be carefully spotted and killed with satellite lasers and 5G antennas, because blackarch is not broken, i love it and some of its tools are those pentesters actually use during real red teaming operations and penetration tests
@po11y if you believe that anonsurf is not transaprent in the way it works, i invite you to read its source code, read it and get what it actually does. it is a bash script, you don’t even need to find its source code online since it is an actual file on your system. so just browse /usr/bin/anonsurf and stay away from kali-anonstealth and other random shit you found online
another important note for you:
privacy and anonymity have something in common but they have very different meanings. don’t confuse technologies designed for privacy with those designed for anonymity, because it is like comparing apples and oranges.
VPN technologies exist to allow private encrypted networks to exist through centralized servers, and an average user can take advantage of them to have extra safety while browsing through a public wifi network or from a totalitarian country, or to access resources (i.e. private servers) that you don’t want to be exposed online, and want to be available only through the VPn (like a company VPN system to access its intranet)
onion routing technologies are a completely different thing, since they are decentralized and way more complex, since their goal is to achieve anonymity. i may even add that it is very insecure to do sensitive operations through an onion routing technolgoy, like doing online banking or accessing the personal profile of a social network, because anonymity has nothing to do with privacy and safety
another thing i may add is that combining VPN and onion routing technologies does not always give better results: the anonymity of tor and the privacy of protonvpn don’t sum up together, they actually sum the number of weaker links in the 2 chains and expand your attack surface
Im just going to say, Im wrong, theres nothing wrong with Anonsurf. It probably just me not using it right.
I dont judge a OS by the tools, I have Ubuntu 20.04 just for simplicity for me running server stuff. I have Arch on another Drive, Kali on another Drive, and Parrot on Another Drive.
Which Do I use the Most? Parrot OS KDE Security. Why? Because you install the tools pretty much the way I want them. How many times do I break a Linux OS? At least Weekly Somthing breaks. Kali Servers arnt up, Or Parrot cant update because Some Dick fAG IS DDOSing my update server. Arch is so updating to where its Bleading old repos that cant be updated causing a chian reaction breaking the entire XORG or Nvidia and everything is the wrong size, the wrong color, or just a KLUSTERFUK of everything… I dont use Blackarch because its not that good. I somtimes use it because I have a HackRF One, and until a few days ago I didnt realize Parrot can just install GNUradio from apt repos and it just works. ubuntu also has a simple way to configure GNUradion, Kali it breaks on. and other Linux boxes I make dont have much sucess either… That PyBomb way to install I dont believe is supported anymore. I feel like Python2 is still supported on Blackarch in somways like maybe that have thier own Python2 repos. I dont know, and things I lack knowdege on is only because I dont have the time to go and investigate every little thing in life. I feel like everything else in my life (not Computer related) that I was born to go around and unf$^k everyones screwups… So the only reason I install 4 linuxes is to have a solid Base to acomplish anything I have to do. And not waste time configuring every thing. Learning every bit, of every piece, of every technology. It seems like at times I have to read an Encylopidia Britanica Volume worth of information just to get silly mudane tasks accomplished.
I respect your work Palinuro and honestly had no idea you wrote Anonsurf, I just tried it again last night and I have to be using it wrong. We have been friends on Facebook for 4 or 5 years I think… At least 3. I only have like 14 people on facebook and your one of them. Ive been talking to you through personal email for at least 5 years now. you always reply to anything I ask  you always give the correct advice, and if I was to get anything sent from you I wouldnt even doubt its 200% legit and I wouldnt even hesitate to think anything malicious was attached. Your an Honest Man and a good man. If I have offended you this is me trying to make amends and correct the wrong I have done.
you always give the correct advice, and if I was to get anything sent from you I wouldnt even doubt its 200% legit and I wouldnt even hesitate to think anything malicious was attached. Your an Honest Man and a good man. If I have offended you this is me trying to make amends and correct the wrong I have done.
I’m not perfect, and I can admit that when most others would not.
Can I send you my bash history so you can see what I tried to, see how I started tor and anonsurf, and what logs would help Identify what Im doing wrong or what ever it is that causes everything to break? when I uise it. it shuts everything down, liek it should, then when go to launch a browser, all I get is that “Sorry this page is not avalible now, please try again later.” on every tab, link, page and ulr I try…
Again Deepest Apologies and I ment no disrespect, maybe my nievitiey has overcome my judgement, or say lack of understanding. I dont know.
Regardless if you wrote Anonsurf or not, You are the only person I would have the confidence to correctly assit me in getting it to work. Thats 100% faith in your capabilities and I can only dream to understand code like you do, and I honestly wish I had the skillset you do in so many ways…
Sorry My Firend
po11y@parrot “awk, polly want a cracker? awk…” LOL
This is not totally true. AnonSurf has random bugs on random machines. Sometimes it is Tor daemon problem sometimes it is systemd. The more things devs want to add, the more bugs devs have to fix. That is normal. People can blame dev team for something wrong in AnonSurf but people likely never blame DE like Mate or XFCE if it doesn’t work or crashes or something. Well i’m not talking about you this but random users i can see on facebook or telegram. There was 1 user got problem of DNS then he changed DNS to 1.1.1.1 and blamed AnonSurf leads to leak DNS.
If you are using latest version of AnonSurf, please create a new topic. I’m the current developer and maintainer of AnonSurf.
We need a better package manager that can do advanced things like synaptic, but very easy to use like play store. I’m fine with working with terminal, but it doesn’t give me a good experience installing apps. I’ll be designing a GUI for it after I finish my 10th grade home school test.
there are transparency switch plasmoids you can download from kde
Os randomly freezes and most times I will have to restart
I have the same issue too. I’m trying to fix it, but the log (/var/log/kern.log) seems normal. Strange…
it is so frustrating, I switched to parrot cause it was meant to be faster than windows but it seems like windows runs better on my laptop
Hey what about adding some BACKUP protocol
[ I was using parrot home edition then switched to Security Editions but i didn’t find any backup stuff and my experience has taught me that in GNU/LINUX you need to have backup and Backup Protocols]
Its pretty easy though
- Add Timeshift for Snapshots and backup
--------------------------------------------------------------------------------------- - A trouble shooting Manual Since Parrot is Debian based it easy to find already PDF or Something in video form for some help because i feel parrot is pretty great for begginers and advance user but if you add some help for begineers it would be great.
------------------------------------------------------------------- - I think These apps should also be pre-installed .
- Timeshift
- GNU Emacs
- Rambox [community edition]
- Kodi
-Stacer [optimizer and cleaner] - Calibre
Yes, I think you are right about adding a trouble shooting manual, for common problems at least, personally I prefer something written to keep my music playing (actually it’s just violin but it helps when I’m working).
I was also thinking maybe Parrot Home should have another look, something different from Security, something elegant and modern maybe, because I don’t like that hackerman mode for a daily OS, this is subjective so…I don’t know if people here agree.
Yes. We also need beautiful GUI for the app store. It might scare new window or mac users away.
It might scare any user, I have just discovered that I have a package manager some days ago and I still prefer the terminal.
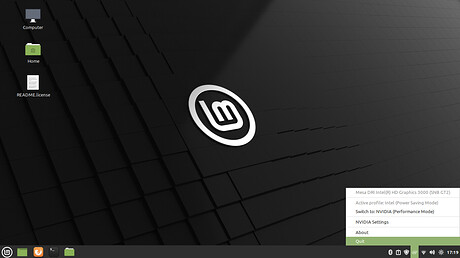
Idea: For Nvidia Optimus
Could Linux Mint’s support for Nvidia Optimus be added in to parrot home edition?
Am by no mean a power user of Linux or a pen/tester. But as a normy I find that feature offered by Mint very user friendly.
I included an image of how clean it looks to open the menu and click the GPU you want to use.
Some distros also have that option available on the Right-Click menu. Which is even better.
I had the same idea 2 years ago. I read the code of Linux Mint’s and found out the structure was like this:
- Get the hardware id → translate to device name. This method can use output of
lspcior parsehwiddb. - From device name, it parses
apt listto get package name that contains supported device. Now this is the critical part: You need a proper list of supported devices for each package. And well, that wasn’t so nice as i checked. So the idea ended up with trouble
So now the question is why don’t Parrot just add the package for Mint
- Mint’s package depends on other package on Ubuntu. It brings us more trouble to package it
- Packages were created for Ubuntu and Mint. So it might not compatible with Parrot. Especially Mint uses Cinnamon and Parrot use KDE / XFCE / Mate
- It is written in Python. I don’t hate Python at all but i don’t like runtime performance. I can do very simple front end with Nim + GTK which could bring the safe effort but has better performance (better here means a lot). Well again, the trouble is not front-end but the backend.
Hello, I think you should add VirtualBox
Vega tool
chrome browser
Solve the problem of the public key signature to make the system more stable There is no need to change the signature key of the system, it must remain stable and stable
There should be updates on the tools and they are arranged well. They are arranged well, but there should be a special section for checking sites in which all the tools needed to check sites are added. You should also add the Dvwa security site
Recommend More DARK THEMES all Parrot GUI.