UPDATE: Editing this post as some of the steps needed to be deleted as they no longer applied
CHANGES:
- Got rid of need for an additional macpriv script (continually changing mac addresses/randomized hostname) by adding it as a function in the start function of anonsurf fork script.
- Further randomized hostname change (updated screenshot)
- Hostname changes back to original on anonsurf stop (fixed a bug where it did not, now works)
*OpenNIC/ParrotDNS default on start (wasn’t in December version)
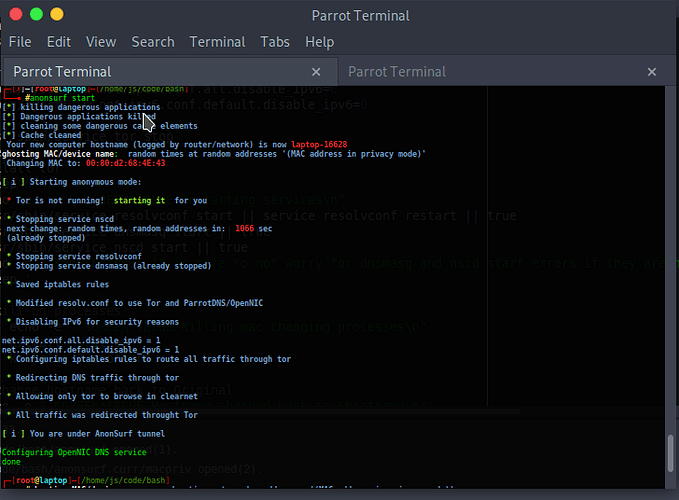
Here is an updated screenshot of AnonSurf modified from/for this tutorial running as a command:
I finished this fork of Parrot Linux AnonSurf the other day & in it I added continually changing randomized mac addresses (changing at continually changing times/addresses using idea from maccleaner script I wrote earlier). The mac changing part is something I had been meaning to add to anonsurf on my machine for a while now.
Added ‘check’ to prevent users from starting it twice (forgetting if they started it)
maccleaner script idea came from using AnonSurf. It was a function I wanted to eventually add to increase local mac address layer privacy logged by WiFi/LAN networks.
Hostname change is in this modified version of AnonSurf as well. Why change your computer’s hostname while using Anonsurf? By default Parrot Linux’s hostname is ‘Parrot’ & this IMHO this could be seen to stand out as your computer name on public wifi/any routers you connect to. The hostname becomes a form of fingerprint and Parrot hostname identifies your computer as a penetration testing distribution. Just as we work to protect our IP address over tor, IMHO we should also hope to protect our hostname/mac address. There are many layers to tracking.
Many Tor user exploits have been used to reveal the client computer mac address (& thus reveal direct identity: google & many other map out home locations of mac addresses; wifi tracking beacons map out mac addresses as you walk with your laptop even if you never connect it broadcasts) using firefox javascript exploits. This is partially an attempt to remedy that.
In addition to the mac/hostname feature I came up with, @dmknght also gave idea to make AnonSurf run as optional systemd service that starts anonsurf at boot (can be easily turned off) so I added that option here too. Completely optional. To find out how, continue reading. This tutorial will cover both subjects. Neither one dependent on the other. Only setup the parts you want to use. (Keep an eye out for new Parrot GUI for Anonsurf in the works @Dmknght is finishing up)
I now run AnonSurf w/the built in mac address randomization at continually randomized times. At first, I wasn’t sure if I would like AnonSurf running at all times (because of google catcha/blocked tor nodes). But this tutorial tells you how to set it up in such a way that you can immediately stop/start/restart it at anytime.
Let’s get started 
Setting Up Modified AnonSurf:
If you already have anonsurf installed all you need to do
is download anonsurf, anonsurf.service, OUI.final, macpriv directly from my github:
1.) Replace /usr/bin/anonsurf with the edited anonsurf script from my github link above.
2.) Put OUI.final in /etc/anonsurf/OUI.final. This file helps ensure you generate completely valid random mac addresses.
3.) Put anonsurf.service file in /etc/systemd/system/anonsurf.service
Now that we have our files in the right locations, let’s add anonsurf as a systemd startup service so we run everything under anonsurf at all times:
sudo systemctl daemon-reload
sudo enable anonsurf.service
sudo start anonsurf.service
Okay you should now have anonsurf running at all times! This is great IMO as you do not have to worry as much about leaks of information as much seeping from your machine. Anytime you want to stop the anonsurf service (say you need to visit a website that blocks tor exit nodes etc) just issue the following to run over normal internet:
sudo systemctl stop anonsurf.service
To start Anonsurf as a service again issue:
sudo systemctl start anonsurf.service
And to do both (stop then restart anonsurf):
sudo systemctl restart anonsurf.service
To check and make sure everything is running properly issue:
sudo systemctl status anonsurf.service
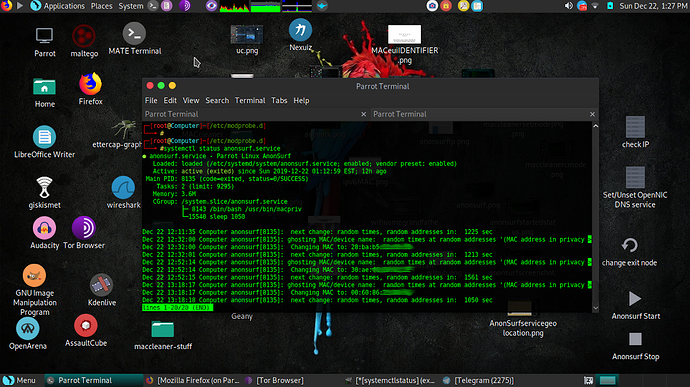
Here is a screenshot which also shows us the history/time differences of mac address changes done by the service:
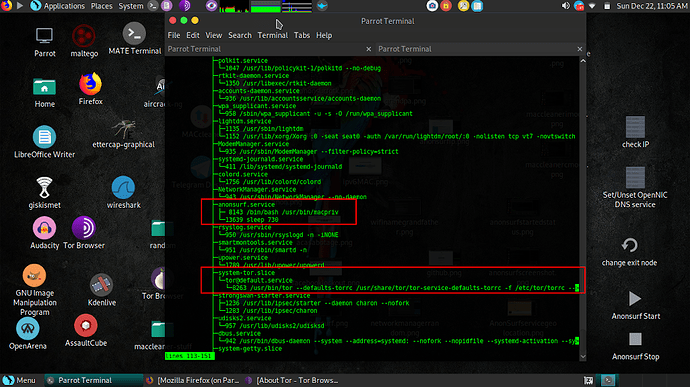
Here is another screenshot looking at the processes running using systemctl:
IMPORTANT:
If you do follow the part of this guide making anonsurf a systemd service, strongly suggest editing /usr/bin/parrot-upgrade script to turn off tor/anonsurf.service when parrot-upgrade command is run, and turn it back on after it finishes. If you do not do this your upgrade will go through the tor network which is not only a potential security issue but also will rate limit your downloads. Not to mention turning off tor for downloads saves the tor network a ton of bandwidth and is a common courtesy to fellow tor users. So please do not upgrade using tor.
Here is an example of edited /usr/bin/parrot-upgrade (will upload this to my github or cut/paste):
#!/bin/bash
echo "Turning off anonsurf.service to speed up process"
echo "and save tor server bandwidth/increase upgrade safety"
echo 'Keep in mind you will be off tor/anonsurf during upgrade'
systemctl stop anonsurf.service
sleep .5
echo '----------------------------------------------------------------------------'
set -e
DEBIAN_FRONTEND="noninteractive"
DEBIAN_PRIORITY="critical"
DEBCONF_NOWARNINGS="yes"
export DEBIAN_FRONTEND DEBIAN_PRIORITY DEBCONF_NOWARNINGS
apt update || echo failed to update index lists
dpkg --configure -a || echo failed to fix interrupted upgrades
apt --fix-broken --fix-missing install || echo failed to fix conflicts
apt -y --allow-downgrades --fix-broken --fix-missing dist-upgrade
echo "Upgrade is finished. Starting anonsurf.service again for you"
systemctl start anonsurf.service
echo '----------------------------------------------------------------------------'
sleep 1
echo "Anonsurf service is now running again."
I hope everything is clear enough for you. If you have any problems/comments/questions, let me know 
Happy surfing!